Vulnerability information from weakdh.org: The Logjam attack allows a man-in-the-middle attacker to downgrade vulnerable TLS connections to 512-bit export-grade cryptography. This allows the attacker to read and modify any data passed over the connection. The attack is reminiscent of the FREAK attack, but is due to a flaw in the TLS protocol rather than an implementation vulnerability, and attacks a Diffie-Hellman key exchange rather than an RSA key exchange. The attack affects any server that supports DHE_EXPORT ciphers, and affects all modern web browsers. 8.4% of the Top 1 Million domains were initially vulnerable.
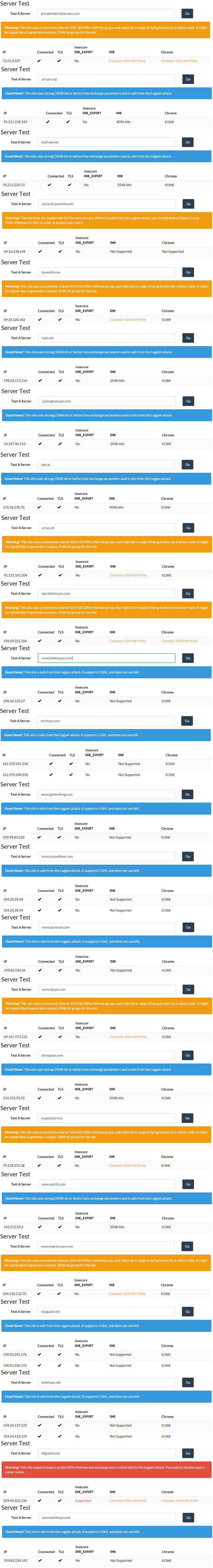
In this article we will post the results of the Logjam test against several, well-known VPN provider websites. Testing was made on May 21, 2015 and the vulnerability is known to the public since May 19.

This means nothing, why don’t you test the vpn servers not the public facing websites
It does mean a lot more than “nothing”.
Maintaining website security is a matter of competence and timely reaction to new threats. A service who isn’t able to keep up with the threats shouldn’t be trusted.
Secondly, most VPN services store valuable customer data on website backends, like VPN credentials and personal identifiable data.
Regarding testing VPN servers, that’s not easy and we haven’t found yet a method to test them. if you know one, share it and we’ll be happy to assess them.